Among the many ongoing concerns for managers of global supply chains has been the proliferation of hostile hackers and the dark money that supports and enriches them.
To counter this phenomenon, several “bug bounty” platforms have surfaced, employing their teams of highly gifted and motivated hackers who strike first to thwart a devastating attack.
“We've learned from years of breaches and lost trust that we need to get smarter to protect our digitally connected society,” says Mårten Mickos, the chief executive officer of HackerOne, one of the premier “hacker-powered” security platforms designed to give supply chain managers the ability to resolve critical vulnerabilities before they can be exploited.
HackerOne is headquartered in San Francisco with offices in London, New York, and the Netherlands.
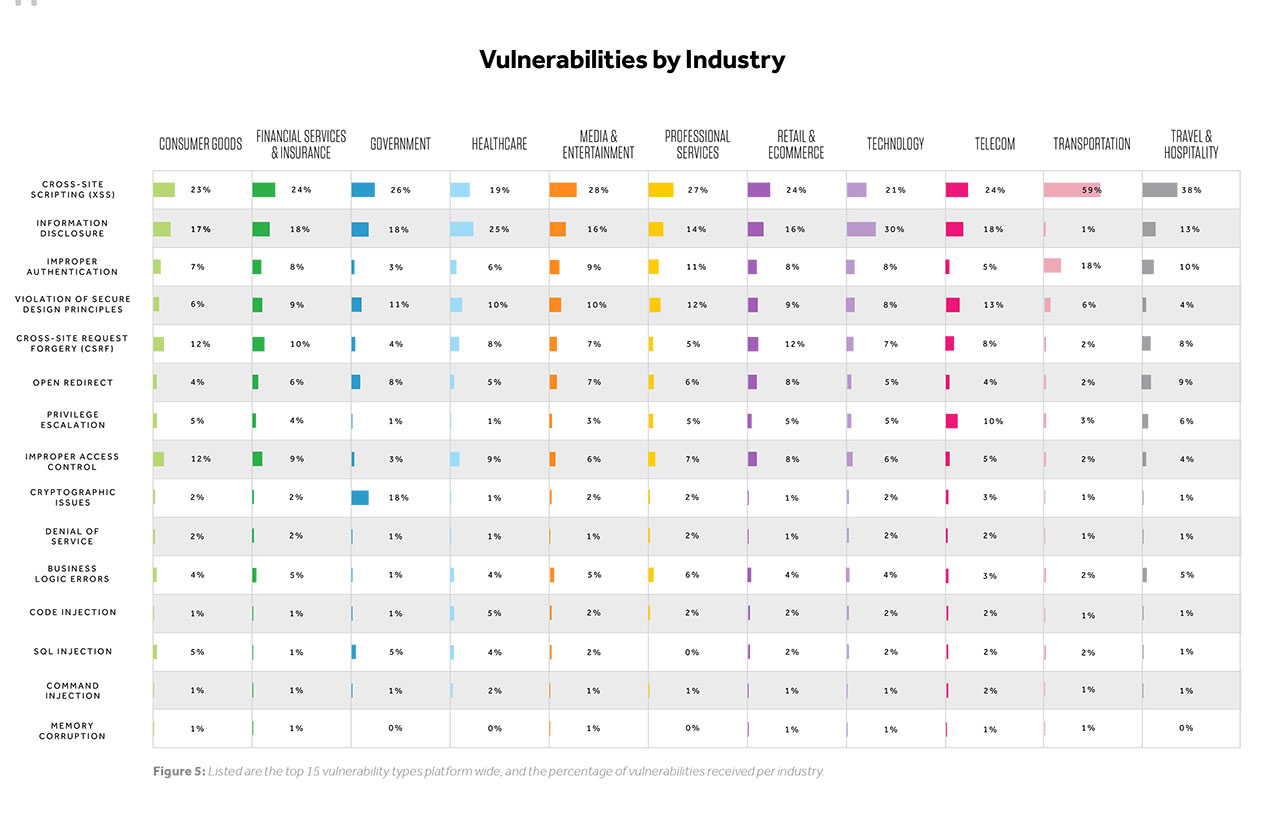
Mickos notes that The Hacker-Powered Security Report 2018 released last week indicates that “bug bounty” programs in particular are no longer limited to tech companies.
“All supply chains irrespective of industry are vulnerable,” he says.
Indeed, among HackerOne's clients are the U.S. Department of Defense, U.S. General Service Administration, General Motors, Google, Twitter, GitHub, Nintendo, Lufthansa, Panasonic Avionics, Qualcomm, Starbucks, Dropbox, and Intel.
“HackerOne customers have resolved over 72,000 vulnerabilities and awarded over $30 million in bug bounties,” observes Mickos.
The Hacker Report was based on over 1,700 responses to the 2017 HackerOne Community Survey, including hackers who successfully reported one valid vulnerability, as indicated by the organization that received the vulnerability report.
“Nearly every company has a digital presence that is susceptible to intrusion, and for that reason, businesses outside of the traditional tech realm—like Shopify—have adopted bug bounty programs,” note researchers. Shopify has paid over $850,000 in rewards, resolved 759 vulnerabilities and has an all-time average first response time of just 3 hours and an average resolution time of just 25 days.

“Trying to address this problem dates back to the 1980s,” says Mickos. “But until recently, it had been ad hoc and spontaneous without any pooling of intelligence and resources. Fortunately, we've ‘gamafied' the system and created critical mass to anticipate these supply chain attacks and reduce companies' exposure while changing the risk landscape.”
SC
MR


Latest Supply Chain News
- Israel, Ukraine aid package to increase pressure on aerospace and defense supply chains
- How CPG brands can deliver on supplier diversity promises
- How S&OP provides the answer to in-demand products
- AI, virtual reality is bringing experiential learning into the modern age
- Humanoid robots’ place in an intralogistics smart robot strategy
- More News
Latest Podcast

 Explore
Explore
Software & Technology News
- AI, virtual reality is bringing experiential learning into the modern age
- Humanoid robots’ place in an intralogistics smart robot strategy
- Tips for CIOs to overcome technology talent acquisition troubles
- Game on: Rethinking change management for the digital era
- Predicting stockouts: Enhancing FMCG resilience through data-driven insights
- Top Performers Investing in, Benefitting from AI
- More Software & Technology
Latest Software & Technology Resources

Subscribe

Supply Chain Management Review delivers the best industry content.

Editors’ Picks